IT Management

UCaaS: Cloud Calling
Cloud Calling provides a secure and resilient platform of feature rich voice communications with true...
Innovating in the Exponential Economy: Chapter 2
For all businesses, innovation is crucial for competitiveness and survival but it is notoriously hard...
How 3 Leading Organizations Took the Fast Path to Cloud
VMware Cloud on AWS Case Studies. Whether you are faced with moving specific applications to the cloud,...
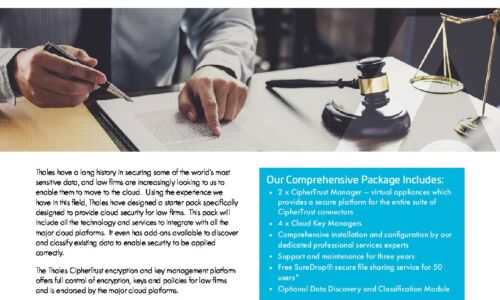
Complete Cloud Security for Legal Firms
Thales have a long history in securing some of the world's most sensitive data, and law firms are increasingly...

A Closer Look at CCPA
How CCPA relates to the access to, deletion of, and sharing of personal information and intends to provide...
Barometer of Cloud Telephony Adoption in Europe
An economy based on distancing has emerged following the COVID-19 crisis that has affected European companies....

A Simpler, Smarter Approach to Mac Management
Mac devices are making massive inroads across every industry, as more companies offer Mac as a choice....
IT Analytics: The Foundation for Cyber Hygiene
Data-driven decision-making (DDDM) uses facts, metrics, and data to guide strategic business decisions...

Change management blueprint for contact centre digital transformation
The COVID-19 pandemic put organisational change into hyperdrive. Businesses were compelled to move to...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.