
CMMC Compliance Guide
On January 1, 2020, the United States Department of Defense (DoD) released its Cybersecurity Maturity...

GSI Report
In This Threat Report The research for our 2021 Global Threat Insights Report was conducted to better...
Redefining Data Loss Prevention
Data doesn't move itself. People—whether they are negligent, compromised or malicious—move data in...

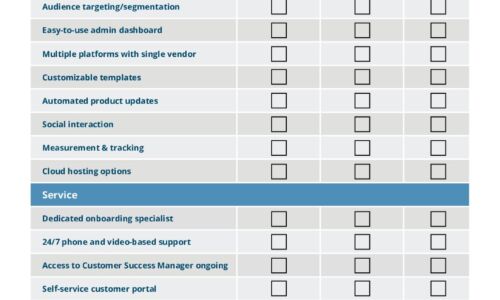
How to Make a More Efficient IT Helpdesk
There's a lot riding on today's Helpdesk Managers and their teams. As organizations have expanded in...
IT Comms Plan Bundle
IT teams need to communicate important messages across their organization – from scheduled maintenance...

Engaging the new digital workforce: A blueprint.
With many employees now working remotely and many others working on-site but at a physical distance,...

The Forrester Wave™: Enterprise Email Security, Q2 2021
In a 25-criterion evaluation of enterprise email security providers, Forrester identified the 15 most...
Phishing Resilience on the Mainframe
Like any other platform, the mainframe is susceptible to cyberattacks. Nefarious practices like phishing...
The Total Economic Impact™ Of ServiceNow Field Service Management
ServiceNow® Field Service Management is a cloud-based solution that connects field service to other...
The Data Breach is Coming from Inside the House
Real-Life Tales of Data Loss, Insider Threats and User Compromise Data doesn't lose itself. People lose...

Making the Grade: End-to-End Security in Education
While students are preoccupied with completing online school assignments and streaming educational videos,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


