Latest Whitepapers
How to Tackle Ransomware by Managing Human Risk
CybSafe's analysis of ICO data finds the number of incidents of ransomware reported has doubled in a...

The Future Is Flexible: Six Areas to Make It Work.
Over 50% of businesses are preparing for long-term, flexible work patterns. But the rush to adopt remote...

Modernize Your Legacy Applications in the Cloud
In the last year, enterprises and industries of all kinds faced rapidly changing business environments...

Five things every business needs to know about GDPR
After years of preparation and drafting, the final t's were crossed and i's dotted on the General Data...

Your Path to Zero Trust
In a business world without perimeters and dominated by remote work, finding a balance between easy collaboration...
ESG Distributed Cloud Series Study 2: Cloud-native Applications
IT organizations are trying to keep their businesses running while migrating to modern, future-proof...
Reimagining Email Security
In the changing landscape, security and risk management leaders must ensure that existing security solutions...

10 Endpoint Security Problems and How to Solve Them
Companies are facing massive cybersecurity challenges – many of which are rooted in the endpoint. In...
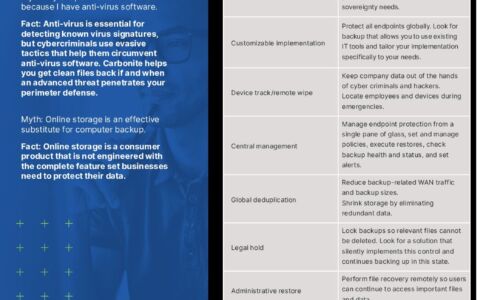
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...

Workday for the Hospitality Industry
With change the only constant today, hospitality leaders need a better way to accelerate digital transformation...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.