Latest Whitepapers
Cyber-resiliency Maturity in Servers
Cyber resiliency is now an essential requirement for any business. Given the threat to data and IT servers,...
2022 Cloud Security Outlook
Developers can't build new products if they have to spend time thinking about security, and security...

Everything You Need to Know About eSignature
How does electronic signature work? Is it legally recognised? What are the main benefits of going paper-free? These...
DDoS attack trends for Q2 2021
Cloudflare's network protects approximately 25 million Internet properties, giving us deep insight into...

How to Leverage O365 for a Zero Trust Strategy
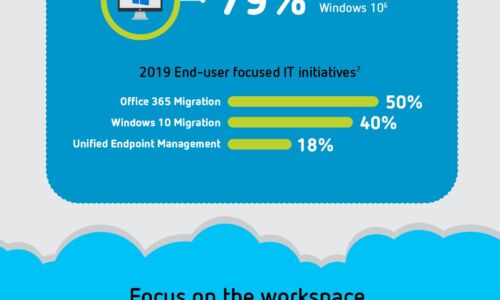
Enterprise adoption of Microsoft Office 365 (O365) skyrocketed to over 258,000,000 users in 2020 and...

Cybersecurity strategies need to evolve.
Over the past 20 years, cybersecurity strategies have primarily focused on protecting the network perimeter...
Can ZTNA replace your VPN?
Compare 3 remote access approaches Seamless remote access enables companies to boost employee productivity...
Hybrid Work: Why it's time to move your on-premises PBX to the cloud
For years, the shift to cloud-based communications services was gradual, with some organizations going...
Would you be ready... if you need to open new offices in 10+ countries?
Midsize companies play a key role in the global economy, driving a large share of job creation, economic...

2021 Digital Trends: Financial Services and Insurance in Focus
During the coronavirus pandemic, the financial services sector became something of an additional emergency...

Transforming the SOC: Building Tomorrow’s Security Operations, Today
When you think of a security operations center (SOC), what comes to mind? Is it an organized team of...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.