NAS

Cyberthreats: A 20-Year Retrospective
Annual threat reports provide an opportunity to look back at significant events of the past 12 months...

7 Leading Machine Learning Use Cases
Machine learning drives results While machine learning has moved beyond the hype to become a meaningful...

The Anatomy of an Insider Threat Investigation: A Visual Guide
For decades, perimeter-based security strategies have been the starting point for most cybersecurity...
The US Customer Experience Decision-Makers’ Guide 2019-20
The US Customer Experience Decision-Makers' Guide is a major annual report studying the CX strategy,...
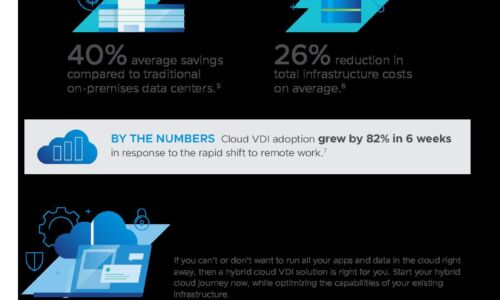
How Cloud Desktops Support Workforce Agility
How fast is the number of devices users employ growing? It has been more than four years since GSMA Intelligence...

User Risk Report
Your cybersecurity posture is only as strong as its weakest link. And in today's people-centric threat...

The Critical Importance of Securing Government Smart Buildings
Over 50% of governments currently have smart building technologies in pilot or production. By 2023, 20%...

Making all the Right Connections
Using digital workflows to blast through barriers, drive loyalty, and accelerate growth. Organizations...

Bilfinger Protects Supply Chain Email Communications
Restores confidence in email and prevents brand misuse through authentication. Cyber criminals use fraudulent...

The Road to Recovery - Growing Your Business in China
The pandemic is fast tracking the digital transformation of organisations in China (and the region) as...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.