Internet of Things (IoT)

Implementing the NIST Zero Trust Architecture with Zscaler
The National Institute of Standards and Technology (NIST) has defined the core components of zero trust...

New Perspectives on Mobile Device Testing at a Global Scale
The old days of just translating the language in your app to make it readable to people in other countries...

DDoS Threat Landscape Report: DDoS Trends from Q3 2022
DDoS attacks are growing larger, stronger, and more sophisticated. In Q3'22, we observed a resurgence...

5G Is Changing the Game - Right Now. Is Your Infrastructure Ready?
Advanced 5G use cases will require a fundamental change in infrastructure before they can scale. As network...

The Business Value of VMware NSX Advanced Load Balancer
With NSX Advanced Load Balancer, teams don't have to choose between overprovisioning and potentially...

How to chose a managed extended detection and response solution
Managed Detection and Response (MDR) solutions are specialized security services that allow an organization...
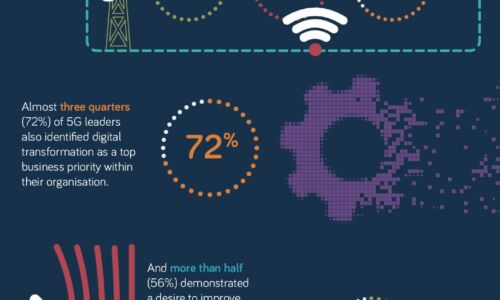
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...

Reinvention Starts with Cloud Migration of Data Infrastructure
Take the complexity out of your data infrastructure For organizations running legacy data infrastructure...
BlackBerry Cyber Suite
The challenge of securing and protecting data and endpoints is not a new requirement, but today it is...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.