Hardware

Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme. Insider threats can...
Cybersecurity: A Short Business Guide
The news often reports on incidents involving large corporations facing massive data breaches where the...

Make your Business Case for Sitecore Content Hub
You need an end-to-end view of your content lifecycle to meet customer expectations and deliver personalized...
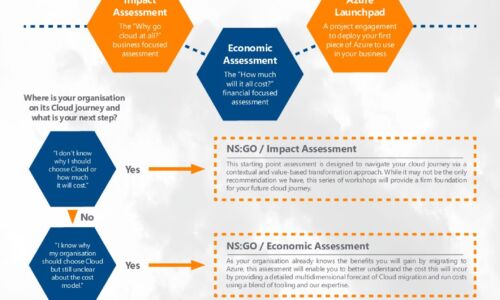
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...

Key Storage Considerations in Determining Optimal Workload Placement
In early 2020, IDC performed in-depth primary research on how organizations determine workload placement...

ESG: Dell Technologies on Demand
Enterprises are actively modernizing their IT infrastructure to support digital transformation initiatives...

How to Save Millions for the New Tomorrow
A guide to finding savings with mission-critical solutions that pay for themselves in months.In today's...

Real-world SLAs and Availability Requirements
Data protection technologies and processes are effective only when you establish clear objectives, then...

Sauce Visual Component Testing
Sauce Visual Component Testing provides organizations the ability to quickly automate the testing of...

Unlocking Collaboration: Making Software Work Better Together
The recent and rapid pace of change in the workplace has required companies to rethink their tools and...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.