Data Reinvention: Business Transformation Through a New Lens
This HBR Report explores the value that data is bringing to organizations and how to avoid the common...
Security Control Guide: Hardened Services Guide
System Hardening is the process of securing a system's configuration and settings to reduce IT vulnerability...

Effortless Service, Happier Customers
This eBook reveals expert insights into how your contact center can effectively implement self-service...

10 Reasons to Adopt E-Signature
The way we work has changed. Modern organisations are putting together new technology systems that allow...
Know Your Options Before Moving To The Cloud
It's imperative for company and IT leaders to understand that the term 'cloud' is very broad and can...
How to Stop Business Email Compromise Threats
While staggering ransomware demands tend to hog the headlines, Business Email Compromise (BEC) is one...

Stay open for business — but closed to cyberthreats
E-commerce relies on always-on connectivity to customers whenever they want to access services. Your...
Data to decisions: A Rulebook to Unlock the Power of Your Data
If any company still questioned the central importance of data to its prospects, the last month has dispelled...
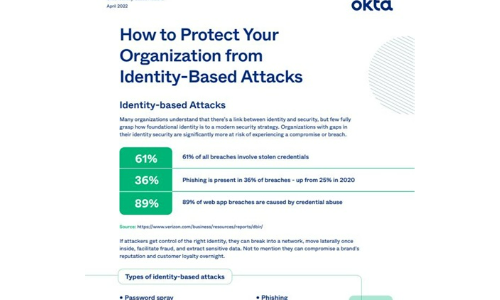
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

Comparing AWS Tools for Cloud Cost Management and Optimisation
Cloud cost management and optimization can become a big challenge as organizations find that the decentralized...
The Total Economic Impact Of PayPal's Enterprise Payment Solutions
PayPal's enterprise solutions deliver enterprise-level credit card and alternative payment processing...
2 Steps to Achieve Endpoint Compliance with KACE® by Quest
Next to ongoing security issues, meeting compliance mandates is one of the biggest challenges IT professionals...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.