
Securing Endpoints Amid New Threats
Giving employees the flexibility to be fully productive while working remotely makes it critical that...

Security Operations Use Case Guide
Responding to security incidents and vulnerabilities is an ongoing process, and you know that reacting...

Three Top Trends in Higher Ed IT for 2021 and Beyond
We've had a tough 2020, but the ability to work and learn online from anywhere has been popular with...
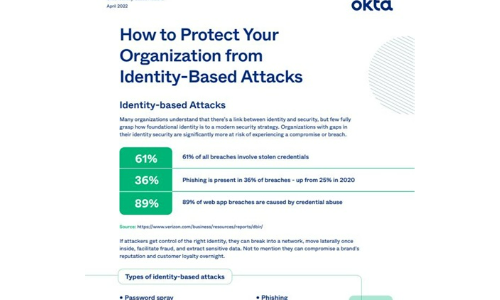
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...
Don’t Diverge—Converge
Digital acceleration is driving the adoption of hybrid IT architectures. These new hybrid environments...

Encryption, Privacy, and Data Protection: A Balancing Act
The Business, Privacy, and Security Mandates for Comprehensive SSL/TLS Inspection. Enterprise IT leaders...

A Guide to Setting Up Your Insider Threat Management Programme
Insider threats are one of the fastest growing categories of risk across organisations today. Companies...

How Proofpoint Defends Against Cloud Account Takeover
Prevent and mitigate potentially devastating cloud account takeovers. Cyber criminals are following businesses...
Reimagining your Workforce Strategy
For all the unhappiness, chaos and uncertainty created by the pandemic crisis, it has also pointed us...

20 Examples of Smart Cloud Security
Smart cloud security provides critical capabilities such as governing access and activities in sanctioned...

Legal Sector Cloud Challenges
The move to the cloud has had a profound effect on all industries, and the legal sector is no exception....

Six Steps to Successful and Efficient Threat Hunting
Rather than waiting for an alert, threat hunters proactively assume that an advanced adversary operates...
Enhancing Microsoft Security with HelpSystems Email Security
Learn how HelpSystems Email Security can enhance Microsoft 365. Microsoft 365 offers tiers of security...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
