Compliance

CX Data Strategy: The Ultimate Framework for Better Customer Experience
Customer loyalty can be fleeting. According to PWC, 32% of customers would stop interacting with a brand...

Threat Brief: Cloud Account Compromise and Takeover
Cyber criminals are getting bolder and more sophisticated with their threats. As more business assets...

Two-Factor Authentication Evaluation Guide
In this guide, you will learn how to evaluate a solution based on: ...

Getting Started with SASE
Secure Access Service Edge: A guide to secure and streamline your network infrastructure As enterprises...
Unlock the Power of Hybrid Cloud with Consistent Operations eBook
Embracing a hybrid cloud operating model creates new possibilities for IT organizations, paving the way...

Learning From The Low-code Playbook
Low-code development is proliferating worldwide — but a rift has opened between the early adopters...

Red Hat for cloud-native development
Application development is a complicated undertaking that requires a complex environment and tools. With...
Accelerating Adobe Experience Cloud Results
Our digital experience experts can help you devise a strategy to maximize your Adobe solutions and get...

The Evolution of Hyperconvergence
This IDC white paper reviews important market trends that have driven rapid growth in global hyperconverged...
An Overview of Insider Threat Management
As organistions move towards a more distributed workforce, the traditional perimeter of the office network...
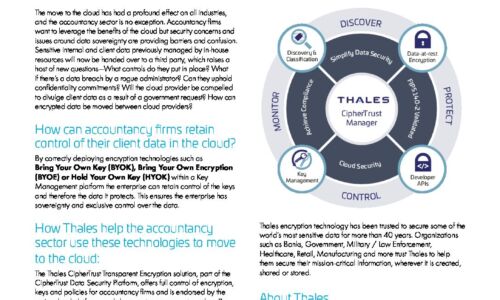
Accountancy sector - Cloud challenges
Accountancy firms want to leverage the benefits of the cloud but security concerns and issues around...

5 Steps to Secure Your Remote Workforce: a Practical Guide
Even before COVID-19, IT and security professionals knew that working remotely was becoming more popular,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.