Cloud
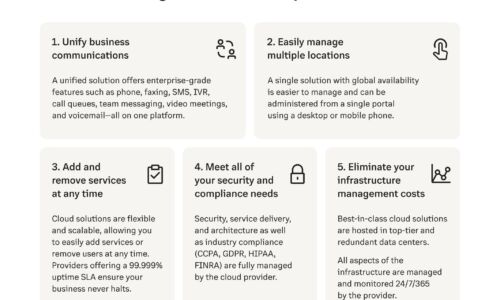
7 Reasons to Switch your On-Premises PBX to the Cloud
Businesses going remote or hybrid require more than what an on-premises PBX can provide. With a cloud...

The SMB Opportunity for MSPs: 2021-2026
According to new research from ConnectWise, MSP industry trends show that SMBs will create over $90 billion...

Unified Promotions: An Offer Hard to Resist
Promotions are no longer a bait to lure customers and clear excess stock, they are now part of retailers'...

QandA: First Steps to a World-class Digital Workspace Experience
Most companies today measure the success of workspace initiatives using tangible cost benefits that are...

Building a Winning Data Strategy
The potential of data to drive business value and create opportunities is well recognized by organizations...
Inside Complex Ransomware Operations and the Ransomware Economy
Ransomware operators have steadily become more sophisticated and more aligned with nation-state actors,...
Why network security matters in healthcare.
The healthcare sector is an attractive target for cyber criminals — it's a honey pot of highly sensitive...

Protect your organization from ransomware
Get a glimpse of the criminal players who operate within the underground ransomware economy. We'll help...

Economist: Signals and Noise: The New Normal in Cybersecurity
Cybersecurity is a top priority for Boards and the C-Suite. Strengthen your security posture with executive...

The Multi-Cloud Maze: 5 Principles for Success
Organisations must now grow and pivot with previously unimagined agility. Enticed by the promises of...

Speed Up Process Change for SAP ERP
The ability to move fast and having a rapid response to change is needed for businesses to innovate faster....

Protecting Every Edge To Make Hackers’ Jobs Harder, Not Yours
Today's users need a network that allows them to connect to any resource from any location using any...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

