Cloud
Enabling the Modern Business Through IT
As the pace of innovation accelerates, customer needs change and industries converge, many companies...

The Forrester Wave™: Enterprise Email Security, Q2 2021
In a 25-criterion evaluation of enterprise email security providers, Forrester identified the 15 most...

How Cloud Enables Modern Management For Midsize Firms
As midsize firms turn to cloud to enable the agility needed to compete in the future of work, most will...

Your Path to Zero Trust
In a business world without perimeters and dominated by remote work, finding a balance between easy collaboration...

Merger and Acquisition IT Integration: Active Directory
Each IT integration project is unique based on the timelines, the makeup of the environment and the goals...

High performance with distributed caching
For many web, mobile, and IoT applications that run in clustered or cloud environments, distributed caching...
The Solarwinds Tipping Point
In December 2020, hackers had broken into several federal government computer networks and the attack...

Unlocking the Secrets of the Hybrid Cloud Leaders
For years, companies have been investing in new technologies, cultivating their culture, and transforming...

7 trainable soft skills for outstanding agents
The average contact centre manager spends 35% of their time looking for coaching opportunities, but only...
Delivering Secure Financial Services for Your Customers in the Cloud
How financial firms build stellar experiences in the cloud From ordering takeout on an app to joining...
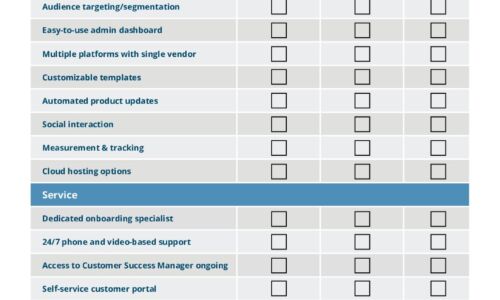
IT Comms Plan Bundle
IT teams need to communicate important messages across their organization – from scheduled maintenance...
Kubernetes for Executives in Telcos
In the coming decade, the telecommunications industry faces large and rapid shifts, from the move to...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

