Cloud

People-Centric Compliance
Your employee collaboration, client communications and promotion and advertisement all flow through digital...
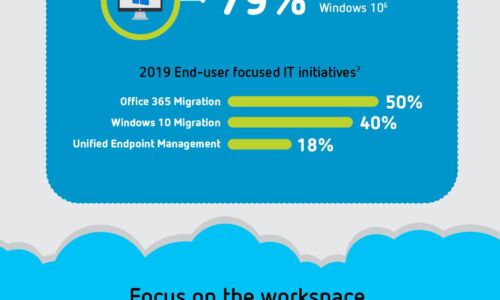
Digital Transformation: A Look Ahead
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...

Microsoft Teams & Telephony
Leveraging calling services from a UCaaS provider, integrated with Microsoft Teams, provides organizations...

A New Trend Explained: What is Multicloud?
Multicloud has become one of the buzzwords of modern IT, yet there's a lack of agreement on what it actually...

NetBackup is Unified Data Protection for the Cloud-Ready Enterprise
As technology evolves, so does NetBackup. This eGuide explores four key use cases that show how NetBackup...
Ransomware Defense for Multi-Site Enterprises: How to Recover Faster
Ransomware is evolving, forcing enterprises to change how they prepare for attacks. While the focus on...

The Economics of Cloud Options in Government
Through the lens of Cloud Economics, explore the risks and benefits of the three ways to upgrade and...

Checklist: How good is your communications system?
How good is your communications system? Today's work takes place in the office, at home, and everywhere...

Maintaining ‘Business As Usual’ In Unusual Circumstances
The phrase 'business as usual' has a reassuring quality. It represents an ideal state in which the company...

Guide to Electronic Signatures
As work evolves to take place outside the four walls of the traditional office, small and midsize organizations...

10 Ways to Fortify Ransomware Recovery Defenses
Ransomware has become a 'cyber-pandemic' that shows no signs of diminishing anytime soon. Your ransomware...

10 Signs It’s Time To Review Your Endpoint Protection
Cyber attacks are increasing in frequency, sophistication, and effectiveness. The ongoing trend of successful...

Migrating to the Public Cloud: Three Success Stories
Organizations find the public cloud appealing for its promises of agility, reduced costs and developer-friendly...

You Got Phished, Now What?
Security leaders work hard to prevent successful phishing attacks. But, despite email security solutions...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.