Cloud Applications
What Separates the Best from the Rest
Some IT organizations have the speed and adaptability to change course quickly when disaster strikes...
DEIB Analytics: A Guide to Why & How to Get Started
Gain insights from RedThread Research on why businesses are focused on diversity, equity, inclusion and...
Intelligent Master Data Management For Dummies
Intelligent Master Data Management For Dummies, Informatica Special Edition, consists of five chapters...

The Evolution of Hyperconvergence
This IDC white paper reviews important market trends that have driven rapid growth in global hyperconverged...

Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme. Insider threats can...
Securing Cloud Applications: Three Ways MFA Can Help
Many cloud applications authenticate users with passwords alone—an alarming notion considering the...

7 Steps to Developing a Cloud Security Plan
Security concerns are top-of-mind for IT executives in light of highly publicized data breaches at a...

File Services with Azure NetApp Files and Cloud Volumes Service
NetApp Cloud Volumes Service and Azure NetApp Files offer something brand new: a fully-managed service...

Multi-Factor Authentication Guide to On-Premise MFA
Despite the advantages of moving to the cloud and in spite of security assurances, there are still organisations...

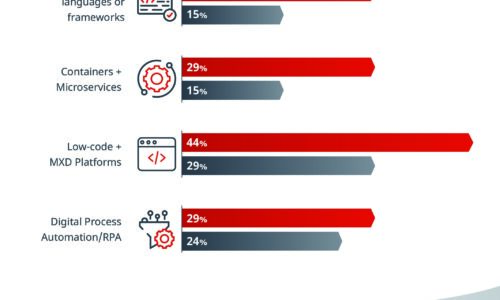
Spotlight: The State of SMB and IT Today
The small and midsized businesses (SMB) continue to be powered by the entrepreneurs who want to build...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



