BYOD

The Beginner's Guide to Dynamic Case Management
What is dynamic case management? Who is using it and how can it help you prepare for the future of work? The...

The Evolving Workplace: Everything as a Service
Innovations in technology disrupt traditional business models. One way companies are already starting...

High performance with distributed caching
For many web, mobile, and IoT applications that run in clustered or cloud environments, distributed caching...

Ponemon Cost of Insider Threats Global Report
Independently conducted by Ponemon Institute External attackers aren't the only threats modern organisations...

Cyber Security for Dummies
Protect your business and family against cyber attacks Cybersecurity is the protection against the unauthorized...

The SMB Opportunity for MSPs: 2021-2026
According to new research from ConnectWise, MSP industry trends show that SMBs will create over $90 billion...
Automated Endpoint Incident Response: An Enterprise Guide
Strong cybersecurity has always been an essential component of a company's digital transformation success....

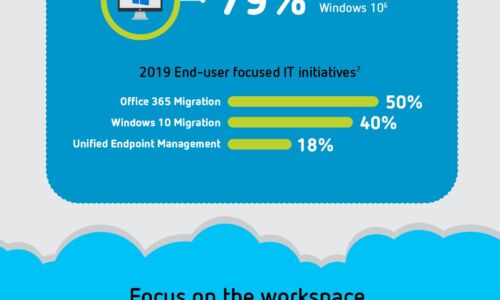
Spotlight: The State of the UK and Ireland Mid-Sized Business and IT
Medium-sized businesses are central to our economies, but this varied market is hard to analyse. So,...

Get Total Endpoint Security with KACE
As an IT professional, you're likely under pressure to manage an increasingly complex environment, while...
The evolution of process automation
Automation has a long and storied history. Today, advancements in artificial intelligence (AI) are spawning...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.