AIM
Effective License Management With A Changing Remote Workforce
Peter Drucker, one of the most widely known and influential thinkers on management, is credited with...
Lacework 2021 Cloud Threat Report, Volume 1
The Lacework Labs team provides quarterly reports focused on risks and threats relevant to cloud services,...

7 Metrics to Measure the Effectiveness of Your Security Operations
You can't improve what you don't measure. To mature your security operations center (SOC) and security...

ITSM Pro: Beyond out-of-the-box
Deliver an AI-powered employee experience across any system with Automation Engine. IT organizations...
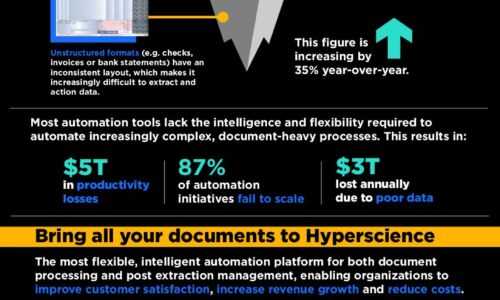
Automatically extract, process, and analyze document data
Transform documents into insights faster with machine learning Escape from manual document processing...
A More Effective CIO-CFO Partnership
How are IT leaders achieving success in a changing world? To find out, Deloitte and Workday surveyed...

The Evolving Role of the CDO At Financial Organisations
Over the past several years, the role of the chief data officer (CDO) has evolved from being security-and...

13 Email Threat Types to Know About Right Now
A cyberattack can affect your business in many ways, depending on its nature, scope, and severity. In...

The Total Economic Impact™ Of Dell EMC Servers For SAP
To run a digital business that is Intelligent and agile, your enterprise requires an IT landscape capable...

Unified Fast File and Object (UFFO) Storage
In this book, you get an idea of the vast potential for unstructured data — and also the infrastructure...

High Security 'to Go'
In the wake of digitalisation, the trend towards mobile work practices is also leading to profound changes....

Successful Microsoft Azure Migration with Quest Data Empowerment Tools
What if there was a model for methodically approaching migration of even your most entrenched relational...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.